The digital defense landscape is being rewoven thread by thread, creating a tapestry where power concentrates in fewer, stronger hands. Like the evolution of any essential craft, cybersecurity is experiencing its own industrial revolution – where artisanal approaches give way to integrated empires.
The Numbers Behind the Narrative
Imagine this: By 2025, organizations worldwide will collectively spend $212 billion protecting their digital assets – a staggering 15% increase from 2024’s already impressive $184 billion commitment. Gartner’s projections aren’t just figures; they’re a testament to our transformed relationship with digital vulnerability.
This financial renaissance emerges from necessity. As our digital lives expand, so do the shadows where threats lurk. And within this expanding universe, approximately 3,000 cybersecurity artisans currently ply their trade – each specializing in different aspects of digital protection.
Consolidation: The New Fashion in Digital Defense
Just as fashion houses absorb independent designers to create comprehensive collections, technology titans are curating complete security wardrobes through strategic acquisitions. Forrester’s Jeff Pollard identifies two distinct patterns in this consolidation runway:
The first resembles haute couture houses acquiring specialized ateliers – established security vendors absorbing innovative boutiques to enhance their creative capabilities. The second mirrors luxury conglomerates diversifying their portfolios – traditional IT powerhouses entering the security space as their legacy markets mature.
Cisco’s breathtaking $28 billion acquisition of Splunk serves as the centerpiece of this collection. This statement piece announces loudly: the future belongs to those who can transform raw security data into intelligence – with AI as the master tailor cutting through complexity.
The Season’s Most Notable Acquisitions

The 2024 lookbook features bold moves that will influence digital protection styles for years to come:
Google’s audacious $32 billion investment in Wiz isn’t merely an acquisition – it’s the digital equivalent of acquiring Dior. This purchase signals Google’s intent to dominate the cloud security aesthetic for generations.
Meanwhile, Palo Alto Networks continues its thoughtful curation by acquiring IBM’s QRadar SIEM for $500 million – similar to a luxury brand adopting a heritage technique to enhance its contemporary offerings.
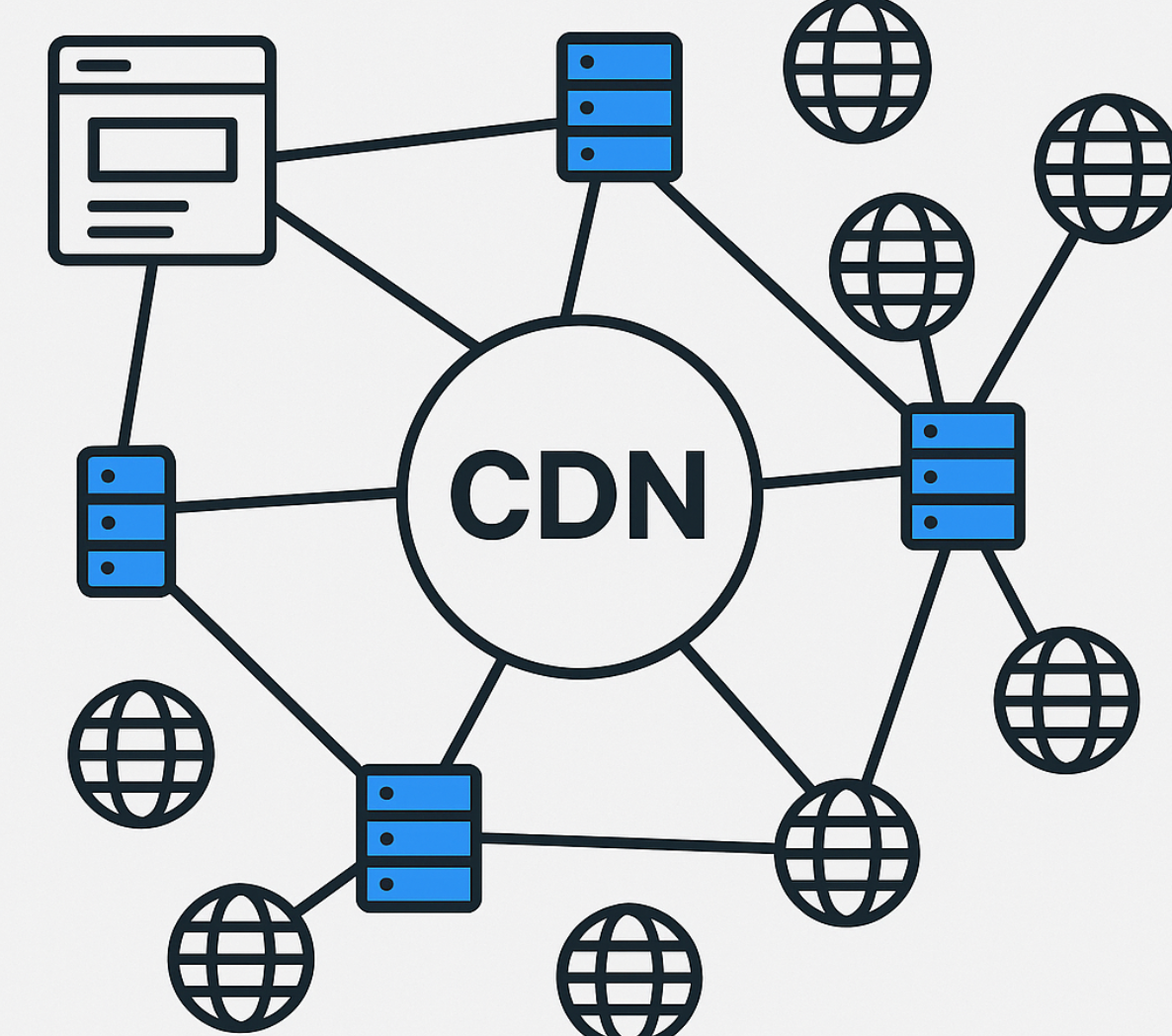
Cloudflare, CrowdStrike, Rapid7, and others have followed suit, each selecting carefully chosen pieces to complete their security ensembles.
The Emerging Security Houses
In every creative field, dominant houses eventually emerge. Cybersecurity is no exception, with Canalys reporting that just twelve vendors now control 53.2% of total spending – up from 51.9% just a year earlier.
The leading houses – Palo Alto Networks (9.5%), Fortinet (6.9%), Cisco (6%), Microsoft (5.7%), and CrowdStrike (3.7%) – have secured their position in this exclusive ecosystem. Like iconic fashion houses, their influence extends beyond market share to shape how we conceptualize security itself.
The Philosophy Behind the Movement
This transformation isn’t merely about business – it’s about creating comprehensive security philosophies. As threats grow increasingly sophisticated, organizations seek integrated approaches rather than piecemeal solutions.
Matthew Ball from Canalys captures this sentiment perfectly: “Threat levels remain elevated. Businesses can’t afford to delay cybersecurity investments.” This urgency drives both spending and consolidation, as companies seek partners who can provide complete protection rather than fragmented defenses.
A New Era Takes Shape
The cybersecurity landscape continues its metamorphosis, driven by the twin forces of integration and innovation. The thousands of specialized vendors are being carefully woven into comprehensive platforms – creating security ecosystems that are greater than the sum of their parts.
For organizations navigating this evolving terrain, the message is clear: the future of digital protection lies not in isolated solutions, but in thoughtfully curated, AI-enhanced security platforms designed to address the full spectrum of modern threats.